Overview
Getting Started
Clusters
PMK CLI
APIs
In Cluster Monitoring
Catapult Remote Monitoring
Platform9 Managed Add-ons
Platform Administration
Workloads & Apps
Support
Powered By

Title
Message
Create new category
What is the title of your new category?
Edit page index title
What is the title of the page index?
Edit category
What is the new title of your category?
Edit link
What is the new title and URL of your link?
Create a AWS Cluster using AWS Assume Role
Copy Markdown
Open in ChatGPT
Open in Claude
Using Assume Role to create AWS CAPI Cluster
Pre-requisites for using Assume Role
For Assume Role to work you need two AWS Accounts:
- Source Account: The AWS account that Cluster API Provider AWS uses to assume a role in a Target AWS Account.
- Target Account: The AWS account into which the role is assumed and where the actual Cluster Resources such as VPC, EC2 Instances etc are created. Note that the target account can also be the same as the source account if needed for some use cases.
Steps:
- Create the required CloudFormation Stack in both Source and TargetAccounts. Steps to create:
- Download the CloudFormationStack template required by PMK.
- Follow the AWS prescribed steps to create CloudFormation Stack using the above template: https://docs.aws.amazon.com/AWSCloudFormation/latest/UserGuide/cfn-console-create-stack.html. Name the CloudFormation Stack as
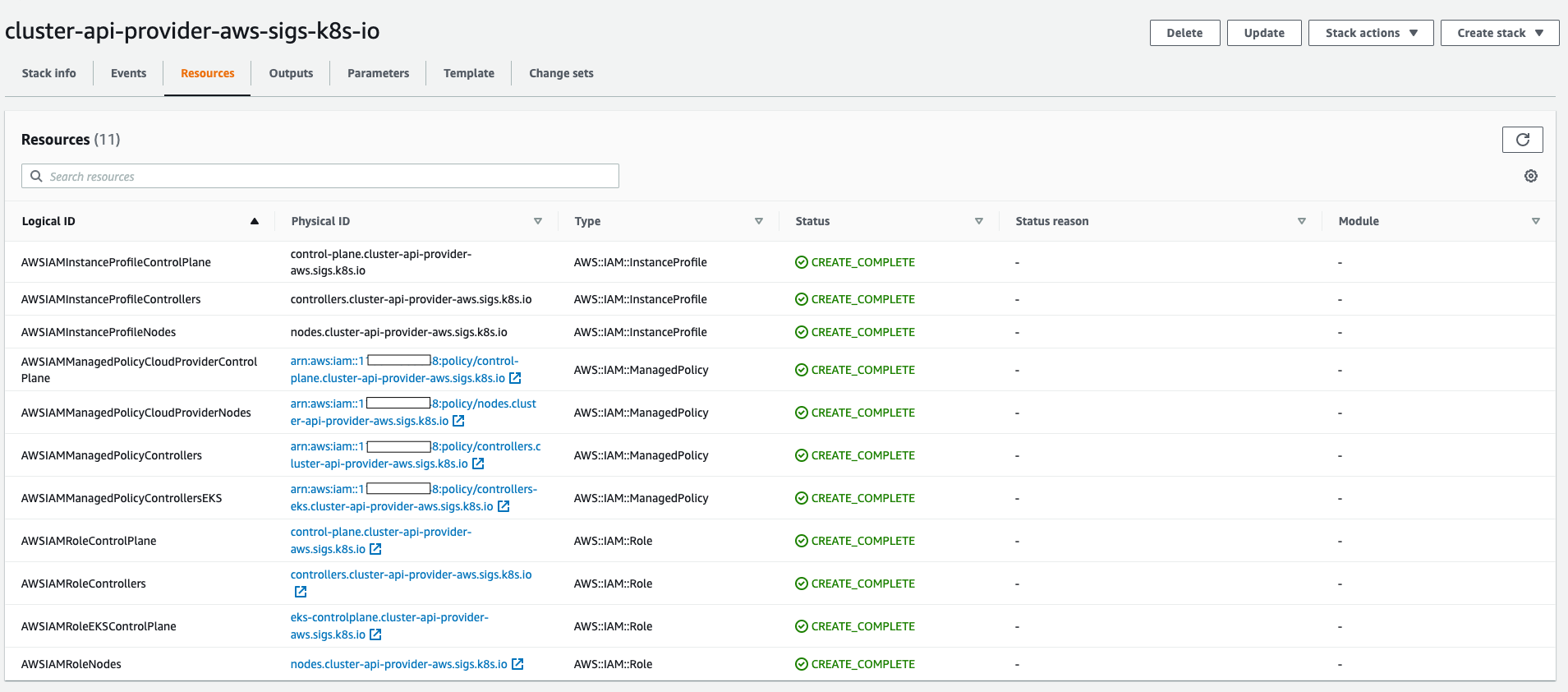
cluster-api-provider-aws-sigs-k8s-io. - Once Created the stack should look like image shown below. All the IAM policies and roles required for CAPI clusters to work should get created.
- Create an AWS Cloud Provider in PMK using the Source Account mentioned above.
- Follow AWS Cloud Provider Management to create it.
- The Source Account User should have IAM policy permissions that enable it to perform sts:AssumeRole operation.
- Source Account user ARN would be like:
"arn:aws:iam::<Source Account>:user/sourceaccountuser".
- Source Account user ARN would be like:
Bash
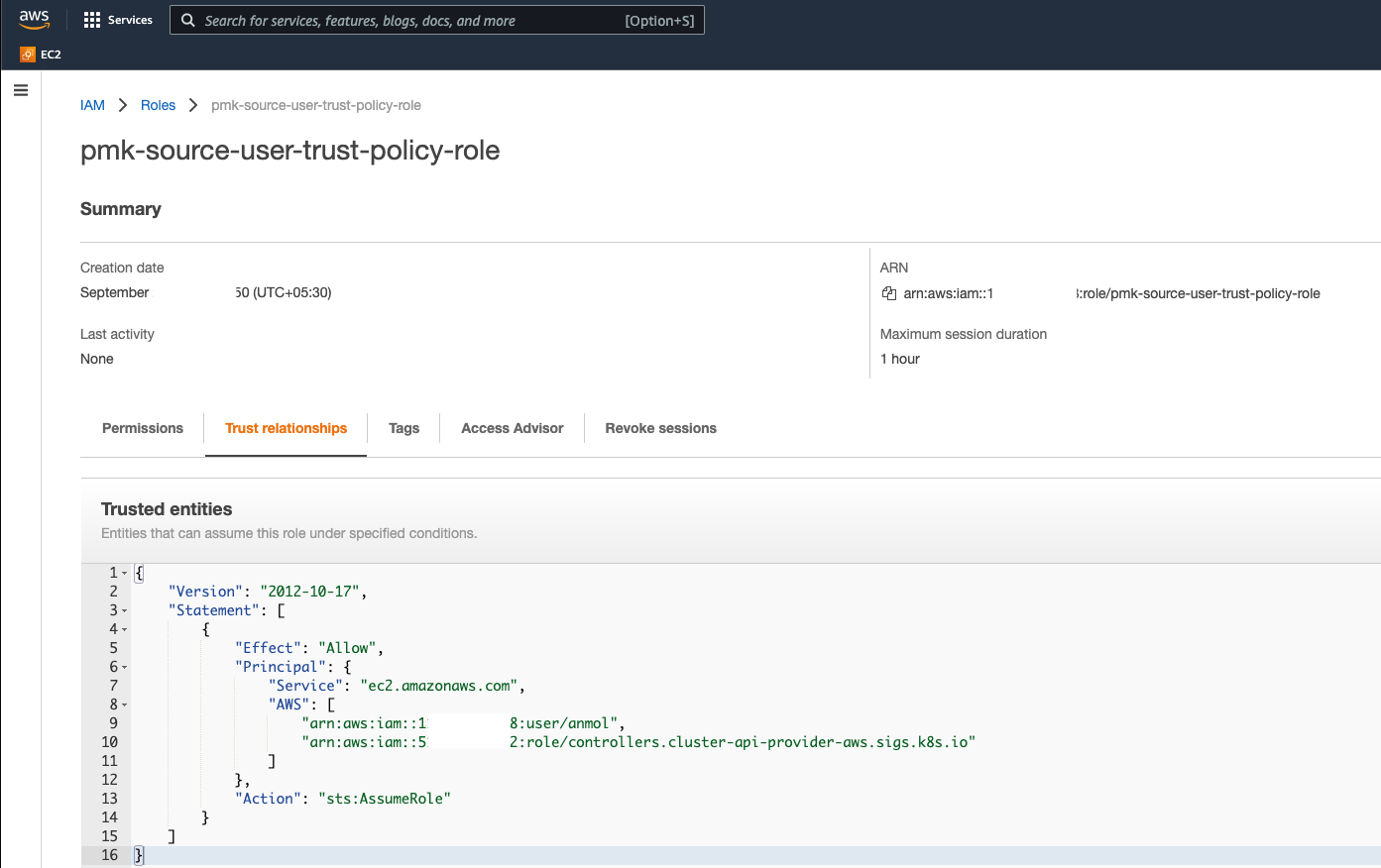
xxxxxxxxxx{ "Version": "2012-10-17", "Statement": [ { "Effect": "Allow", "Action": "sts:AssumeRole", "Resource": "*" } ]}- Create a AWS Role of type Custom Trust Policy in the Target Account to allow the source user to assume into it by setting a trust policy.
- Note the role
"arn:aws:iam::<Source Account>:role/controllers.cluster-api-provider-aws.sigs.k8s.io"is created in the step 1 of creating the CloudFormation Stack in the Source Account.
- Note the role
Bash
xxxxxxxxxx#pmk-source-user-trust-policy-role { "Version": "2012-10-17", "Statement": [ { "Effect": "Allow", "Principal": { "Service": "ec2.amazonaws.com", "AWS": [ "arn:aws:iam::<Source Account>:user/sourceaccountuser", "arn:aws:iam::<Source Account>:role/controllers.cluster-api-provider-aws.sigs.k8s.io" ] }, "Action": "sts:AssumeRole" } ]}Once created the the Target Role should look like:
Creating the Cluster
Using the resources created in pre-requisite steps, create the cluster.
- Navigate to Infrastructure > Clusters
- Click Add Cluster
- Choose Amazon Web Services
- Select New Generation AWS Cluster
- Click Start Configuration
- Enable the AWS Assume Role Toggle
- Choose the already created Source Account Provider.
- Enter the Target Role ARN
Example:
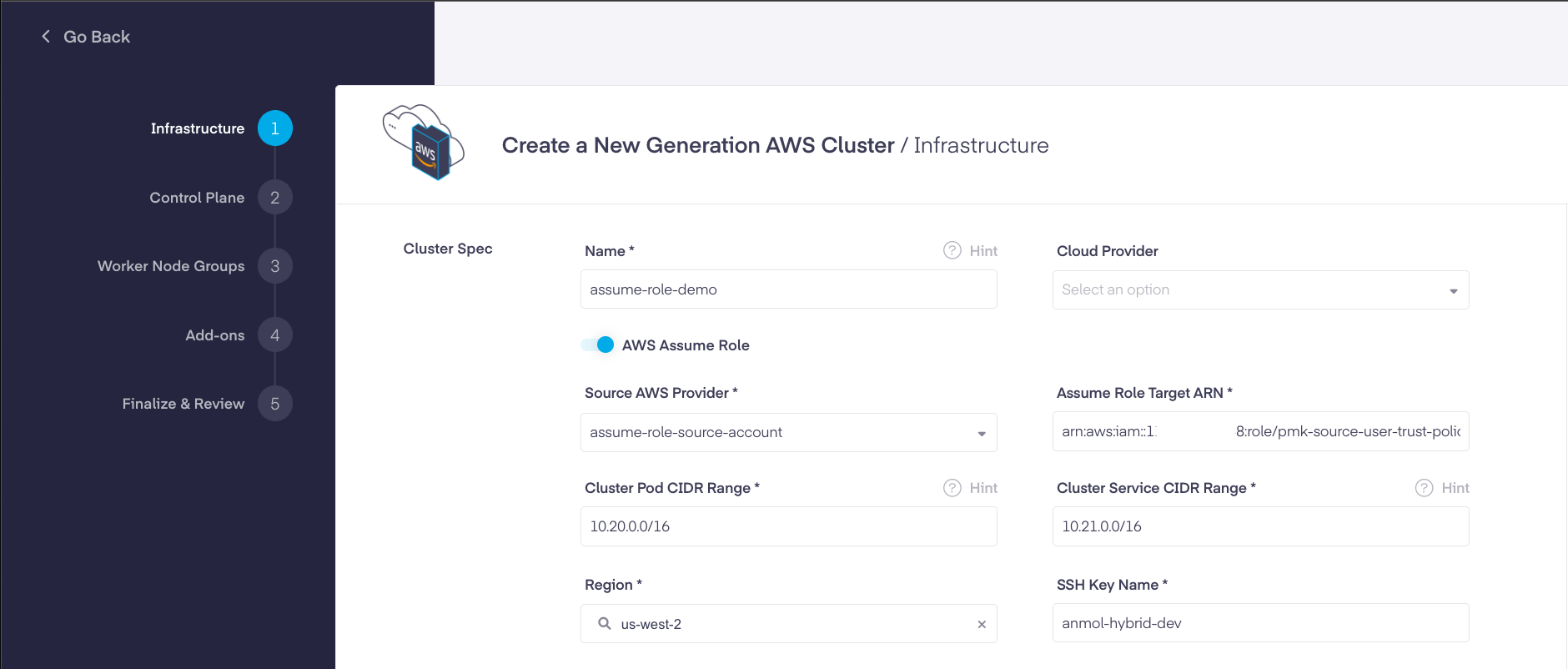
Go to Create an AWS Cluster for more details on further cluster creation steps.
Type to search, ESC to discard
Type to search, ESC to discard
Type to search, ESC to discard
Last updated by Anagha Pamidi on Jan 26, 2026
Was this page helpful?
Next to read:
AWS Node GroupsDiscard Changes
Do you want to discard your current changes and overwrite with the template?
Archive Synced Block
Message
Create new Template
What is this template's title?
Delete Template
Message